Configuring SSH on Cisco IOS
Once you start working with Cisco routers, you may wonder how you set up a SSH connection to a router. Five easy steps to do it are below.
We’ll take a Cisco 881 router. Steps to set up a connection to a different router (1841, 2800, 3825, etc.) or a switch (2900, 3500, 4800, etc.) are pretty much the same, though interface configuration can be a little different. (Setting up a SSH connection to Cisco ASA firewalls is described in the article “Cisco ASA basic Internet access“)
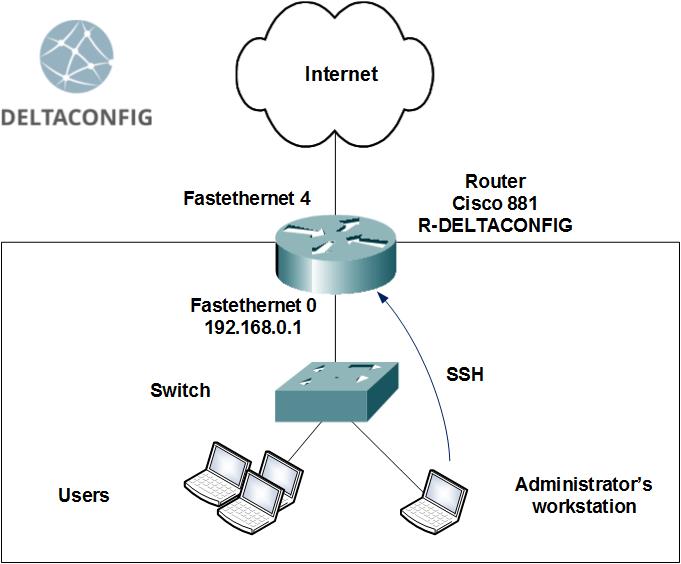
So, we have on hand
- a Cisco 881 router,
- an administrator’s workstation,
- several PC’s in the office LAN,
- a switch connecting the PC’s together on the LAN.
The task is to configure a secure connection to the Cisco router via SSH and provide a means of secure remote control.
Step 0. Configuring an interface
The router should have one interface, the one that is going to be used for remote control, enabled. In our case, it’ll be a LAN Fastethernet 0 interface.
Quick reference:
A Cisco 881 router has one Layer 3 interface, called Fastethernet 4, and a built-in switch with four Layer 2 interfaces (Fastethernet 0 to Fastethernet 3). Each of those four interfaces can carry traffic to only one virtual Layer 3 interface (Vlan).
We choose an IP address for the router control interface from the office LAN pool — say, 192.168.0.1. Next, we configure Vlan 1 virtual interface to have this IP address. After that, we bind it to one of the physical interfaces of the router (Fastethernet 0) and enable it with a no shut command.
The outline of the required configuration is
IP address → Vlan X interface → Fastethernet Y interface
We set the IP address for the Vlan 1 interface
R-DELTACONFIG (config)#
interface Vlan 1
ip address 192.168.0.1 255.255.255.0
no shutsown
and bind Vlan 1 to the Fastethernet 0 physical interface
R-DELTACONFIG (config)#
interface Fa 0
switchport access vlan 1
no shutsown
We’re doing the last action to check that the configuration is correct. By default, Vlan 1 is binded to each of the Layer 2 interfaces. The configuration will only have this line for Vlan‘s other than 1.
Next, we check if the newly created interface is accessible from the router itself and from the office workstations, say, from the administrator’s workstation. A simple ping will do. Of course, the Fastethernet 0 router interface has to be connected to the LAN switch (or directly to the administrator’s workstation), and the workstation address has to be in the same network as the router interface address (for example, 192.168.0.10).
Step 1. Setting up an admin account
For the remote control, we create an admin account, if none has been created before.
R-DELTACONFIG (config)#
username admin secret *****
Change asterisks to your admin account password.
Important!
A good password will have both uppercase and lowercase characters, numbers and special characters, no less than 8 characters total.
Step 2. Setting a privileged mode password
By default, a user connected to Cisco command-line interface has user access rights and can only read some device parameters and technical information. The command-line prompt in the user mode is:
R-DELTACONFIG>
To list the router configuration and change it, type enable
R-DELTACONFIG> enable
R-DELTACONFIG#
By default, a privileged mode is not password-protected, and any user connected with a console cable (see more on the console cable connection in this article) can enter the configuration mode. However, a remote user (via ssh or telnet) with no preset privileges, which is our case, cannot access the configuration mode.
We set a privileged mode password (command-line prompt is #) from the configuration mode (conf t).
R-DELTACONFIG (config)#
R-DELTACONFIG (config)# enable secret ******
This password is the same for all users.
A little bit more about about the configuration modes is written in this article
Step 3. Enabling remote control
To enable the remote control, specify the authentication method with login local
R-DELTACONFIG (config)#
line vty 0 4
login local
After this step, you can connect to the router using telnet protocol, provided that the router control interface is accessible to the user via the network. For that, run from the command prompt at the administrator’s workstation
C:\Documents and Settings\***>telnet 192.168.0.1
You will be prompted to enter your username and password, as configured in step 1. On authorization, you will be able to control the router in user mode (> prompt). For the privileged mode (# prompt), type enable and enter your password from step 2.
Step 4. Configuring SSH
Telnet protocol (TCP port 23) transmits all commands and configuration data in plain text, which is potentially unsafe. For a secure connection, use SSH protocol (TCP port 22).
To configure an SSH connection, set an arbitrary domain name, generate a cryptographic key and enable SSH protocol version 2.
R-DELTACONFIG (config)#
ip domain-name deltaconfig.com
crypto key generate rsa
Choose the size of the key modulus in the range of 360 to 2048 for your
General Purpose Keys. Choosing a key modulus greater than 512 may take
a few minutes.
// when prompted, type 1024
How many bits in the modulus [512]: 1024
% Generating 1024 bit RSA keys, keys will be non-exportable...[OK]
ip ssh ver 2
After this step, you will be able to connect to your router using an SSH client of your choice. For example, you can use PuTTY.
Step 5. Enabling SSH-only connections
To prevent telnet connections to the router, type:
R-DELTACONFIG (config)#
line vty 0 4
transport input ssh
After that, you will be able to access the Cisco command-line interface only via SSH.
Additionally, you can restrict the router/switch remote control to certain IP addresses only. For instructions, look at this article.
Important!
Access your devices in a secure way. Only use secure connections and limit the distribution of remote control privileges.
Important!
Don’t forget to save your changes to the device configuration with write or copy run start. Otherwise, the changes will be discarded on reboot.
R-DELTACONFIG#write
Building configuration...
[OK]
This article was written by Alexey Yurchenko